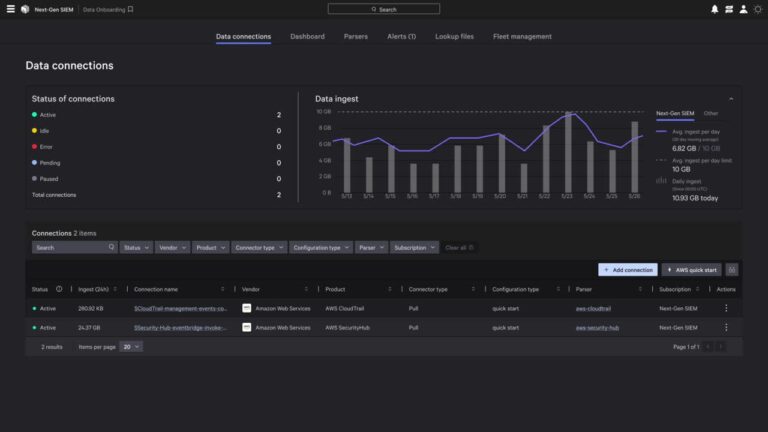
Transform AWS Security Operations with Falcon Next-Gen SIEM
CrowdStrike is redefining how SOC teams turn cloud data into actionable intelligence by unifying speed, scale,…
CrowdStrike is redefining how SOC teams turn cloud data into actionable intelligence by unifying speed, scale,…

Join hosts Paul Sweeney and Vonnie Quinn as they discuss markets, the retail space and more…

That report cited comments made by a RealPage vice president, Jay Parsons, at a meeting with…

A two-day summit of EU and African Union leaders in Luanda, Angola has drawn to a…

And a term anyone with or around kids seems to both know about … and be…

On this episode of Stock Movers, we look at some of the week’s biggest gainers and…

For months, there has been talk of an impending AI bubble burst. Investors fear that the…

DeepSeek-R1’s Intrinsic Kill Switch It is also notable that while Western models would almost always generate…

Berkshire Hathaway’s latest quarterly filing reveals the company accumulated a US.3 billion stake in Alphabet over…

President Putin inspected a dancing humanoid robot at an exhibition in Moscow on Wednesday with wary…

While the battle for Pokrovsk rages, the entire front line hangs in the balance. Military expert…

Nvidia, the world’s most valuable company, is set to deliver a quarterly report Wednesday that could…

Online gaming giant Roblox has just announced it will start checking users’ ages from early December…

In Saudi crown prince’s first visit to the US since the killing of journalist Jamal Khashoggi…

Anthropic’s Threat Intelligence team recently uncovered and disrupted a sophisticated nation-state operation that weaponized Claude’s agentic…

Israelis Demand Oct 7 Inquiry in Massive Tel Aviv Protest Thousands of Israelis gathered in Tel…

AI has collapsed the vulnerability exploit lifecycle. Adversaries now discover, weaponize, and exploit exposures across hybrid…

Zero-Day Vulnerability in Windows Kernel CVE-2025-62215 is an Important elevation of privilege vulnerability affecting Windows kernel…

As nearly half of all Australians say they have recently used artificial intelligence (AI) tools, knowing…

Over the course of two months, Bloomberg Businessweek conducted interviews with 18 people who either have experienced delusions…

Apple has been struggling to fix Siri since it’s inception in 2011, but today they find…

Afghanistan’s Taliban has issued a stern warning to Pakistan after peace talks in Turkey failed. Taliban…

Most exposure reporting is still slow, error-prone, and disconnected from reality. Analysts spend hours collecting and…

James Dewey Watson, who helped reveal DNA’s double-helix structure, kicked off the Human Genome Project, and…